What is SQL Injection and how it works?
SQL Injection is a serious web security vulnerability that allows attackers to manipulate database queries by injecting malicious SQL code into user input fields. It works by exploiting applications that fail to properly validate or separate user input from executable SQL commands.
SQL Injection is a type of cyberattack in which an attacker inserts malicious SQL (Structured Query Language) code into an application’s input fields in order to manipulate the database behind the website or software.
It is one of the most common and dangerous web application vulnerabilities because many websites rely on databases to store sensitive information such as usernames, passwords, personal data, financial records, and business information.
When input fields are not properly validated or sanitized, attackers can exploit them to execute unauthorized database commands. SQL Injection does not usually target the database system itself but rather poorly coded applications that interact with the database.
To understand how SQL Injection works, it is important to first understand how web applications communicate with databases. Most dynamic websites use a database management system such as MySQL, Microsoft SQL Server, or Oracle Database to store and retrieve data.
When a user submits information through a login form, search box, or contact form, the application sends a SQL query to the database. For example, during login, the application might send a query like: SELECT * FROM users WHERE username = 'user' AND password = 'pass'; The database checks if the credentials match a record and grants access if they do.
If the application directly inserts user input into the SQL query without proper validation, it creates an opportunity for SQL Injection.
An attacker takes advantage of this vulnerability by entering specially crafted input instead of normal data. For instance, instead of entering a normal username, the attacker might input something like: ' OR '1'='1. When inserted into the SQL query, it could transform the statement into: SELECT * FROM users WHERE username = '' OR '1'='1' AND password = ''. Because the condition '1'='1' is always true, the database may return all user records or allow login without a valid password.
This is a simple example, but it illustrates the core idea: malicious input changes the structure of the SQL query so that it performs unintended actions.
SQL Injection attacks can have severe consequences. Attackers may retrieve confidential data, including usernames, passwords, email addresses, or credit card information. They can modify or delete database records, deface websites, or even gain administrative control of the application.

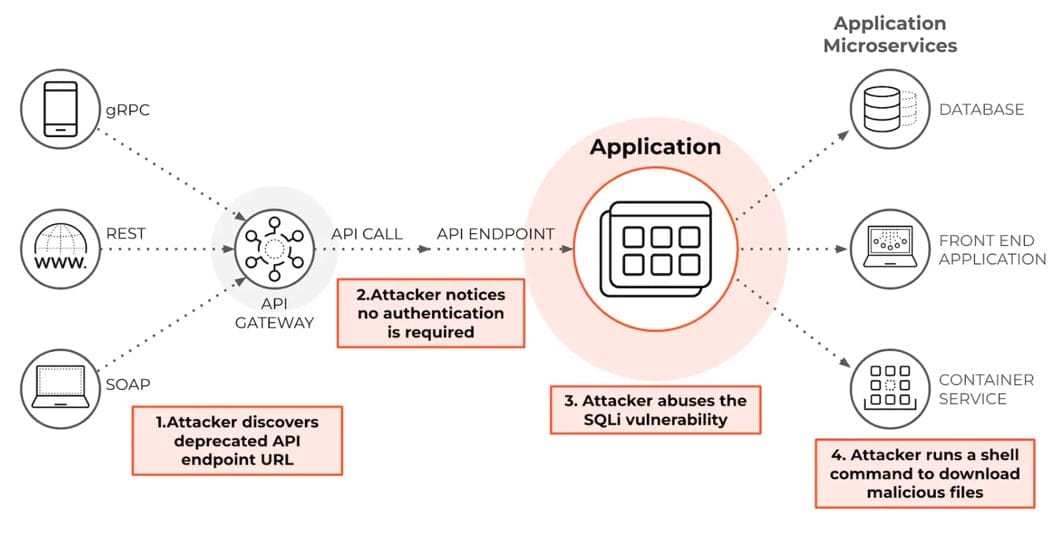
In some cases, advanced SQL Injection attacks allow attackers to execute operating system commands on the server, leading to complete system compromise. This makes SQL Injection a critical security risk for businesses and organizations that store sensitive data online.
There are different types of SQL Injection attacks. The most common is in-band SQL Injection, where the attacker uses the same communication channel to launch the attack and receive the results. This includes error-based SQL Injection, where database error messages reveal useful information, and union-based SQL Injection, where attackers use the UNION SQL operator to combine results from multiple queries.
Another type is blind SQL Injection, where the application does not display database errors or results directly. Instead, attackers infer information by observing differences in application behavior, such as changes in page content or response time. A more advanced type is time-based blind SQL Injection, where attackers send queries that delay the database response, helping them determine whether their injected condition is true or false.

SQL Injection typically occurs because of poor coding practices. When developers directly concatenate user input into SQL statements without proper filtering, escaping, or parameterization, the system becomes vulnerable. Modern programming frameworks and database libraries provide secure methods to prevent SQL Injection, such as prepared statements and parameterized queries.
These techniques separate SQL code from user input, ensuring that the input is treated strictly as data and not as executable code. Input validation, stored procedures, and the principle of least privilege—where database accounts have only minimal required permissions—also help reduce the risk.
Preventing SQL Injection requires a combination of secure coding practices and security controls. Developers should always use parameterized queries or prepared statements. Web application firewalls can help detect and block suspicious requests. Regular security testing, such as penetration testing and code reviews, can identify vulnerabilities before attackers exploit them. Keeping database systems and web frameworks updated is also essential to address known security flaws.
In conclusion, SQL Injection is a serious web security vulnerability that allows attackers to manipulate database queries by injecting malicious SQL code into user input fields. It works by exploiting applications that fail to properly validate or separate user input from executable SQL commands.
The consequences can include data theft, data loss, unauthorized access, and even full server compromise. However, with proper coding practices, input validation, parameterized queries, and security monitoring, organizations can effectively protect their systems from SQL Injection attacks and maintain the integrity and confidentiality of their data.





