What Is SQL Injection?
SQL injection attacks can cause serious damage to organizations and users. Attackers can steal personal data, financial records, and login credentials.
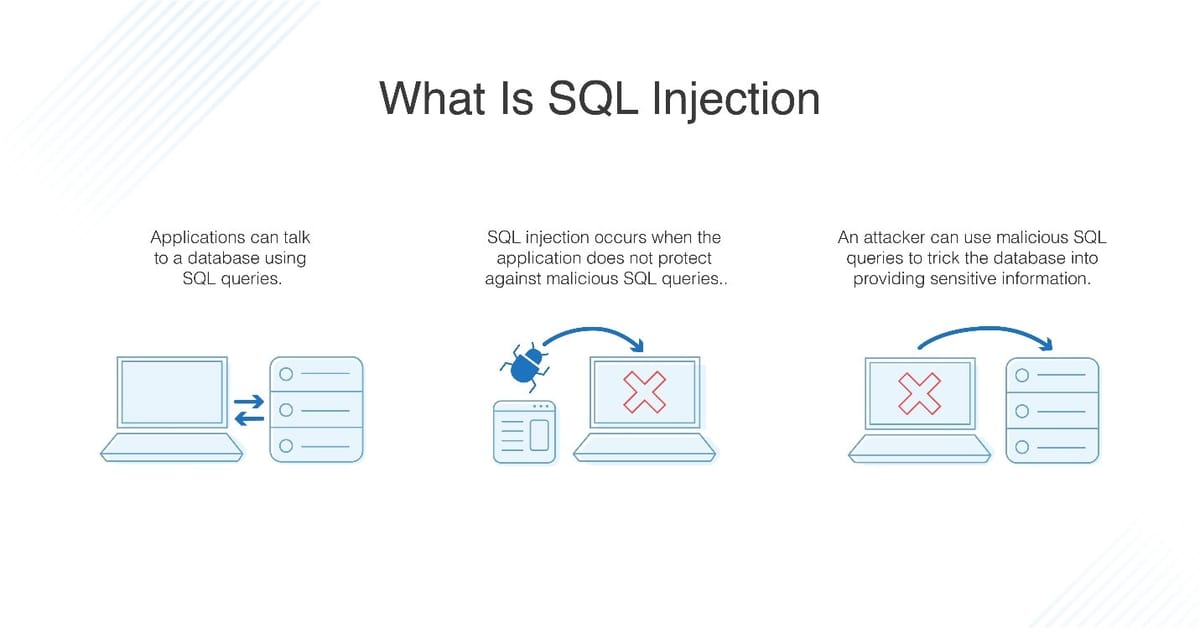
SQL injection is one of the most common and dangerous web security vulnerabilities found in modern applications. It occurs when an attacker is able to insert or “inject” malicious SQL code into a database query through user input.
If successful, the attacker can access, modify, or delete sensitive data, bypass authentication, and even take full control of the database. Understanding SQL injection is essential for developers, website owners, and anyone concerned about web security.
What Is SQL Injection?
SQL injection is a type of attack that targets databases used by web applications. Most websites use databases to store information such as usernames, passwords, customer records, and transaction details.
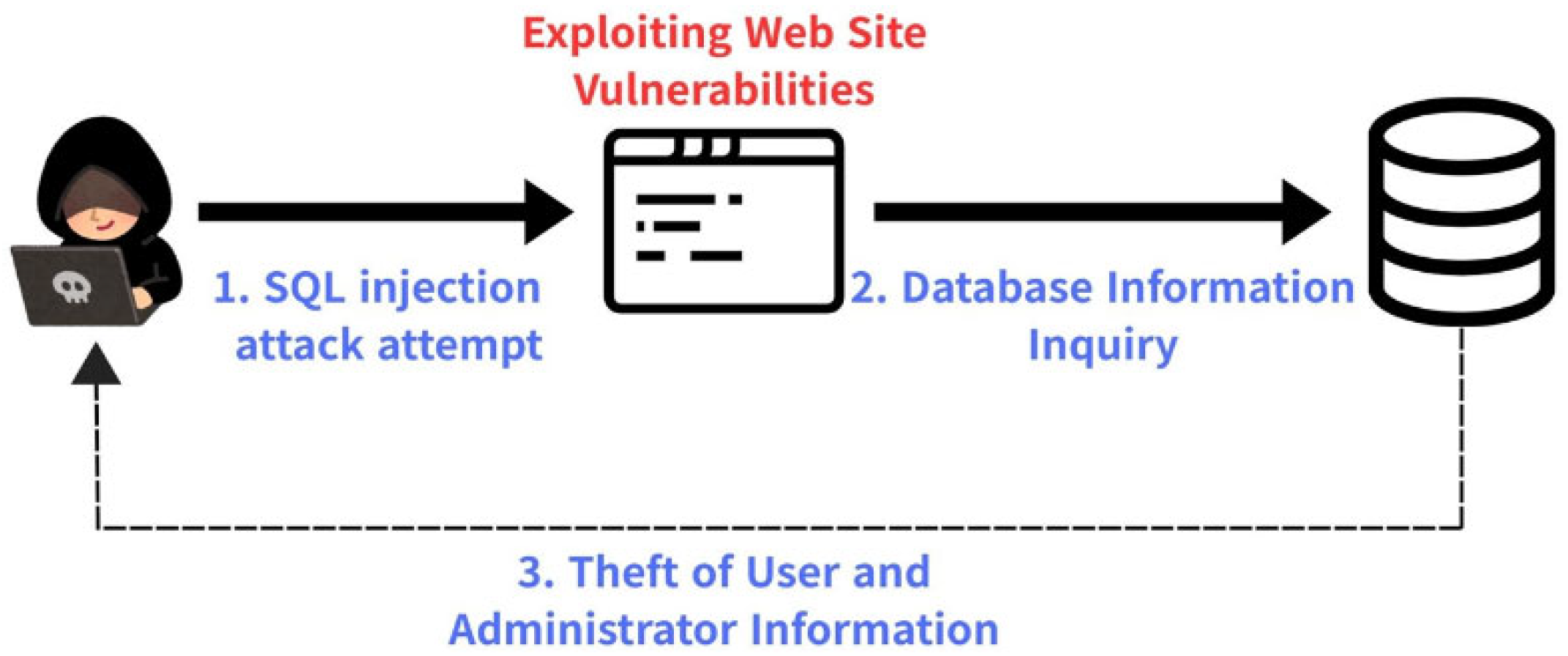
When a web application does not properly validate or sanitize user input, attackers can manipulate SQL queries that the application sends to the database. This allows them to execute unintended commands and retrieve data they should not have access to.
How SQL Injection Works
SQL injection usually happens through input fields such as login forms, search boxes, contact forms, or URL parameters. For example, if a website directly inserts user input into a SQL query without validation, an attacker can input special SQL characters or commands.
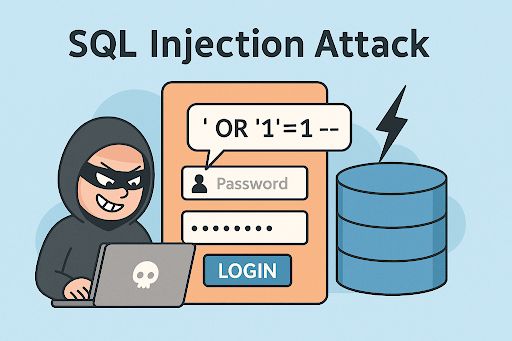
The database then executes this altered query, often returning confidential data or allowing unauthorized actions. This makes SQL injection especially dangerous for websites that handle sensitive user information.
Common Types of SQL Injection
There are several types of SQL injection attacks. In-band SQL injection is the most common and occurs when attackers use the same communication channel to both launch the attack and retrieve results. Error-based SQL injection relies on database error messages to gain information about the database structure.
Union-based SQL injection uses the SQL UNION operator to combine results from multiple queries. Blind SQL injection happens when the application does not display errors, forcing attackers to infer information through true or false responses or time delays.
Why SQL Injection Is Dangerous
SQL injection attacks can cause serious damage to organizations and users. Attackers can steal personal data, financial records, and login credentials. They can modify or delete database contents, leading to data loss and service disruption.
In some cases, SQL injection can allow attackers to gain administrative access to systems, install malware, or move deeper into the network. The financial and reputational damage caused by such attacks can be severe.
Real-World Examples of SQL Injection
Many high-profile data breaches have been linked to SQL injection vulnerabilities. Poorly secured websites, outdated software, and lack of security testing are common causes.
Even today, SQL injection remains a top security risk because many applications still fail to follow secure coding practices. Small websites and large enterprises alike are vulnerable if proper precautions are not taken.
How to Prevent SQL Injection
Preventing SQL injection starts with secure coding practices. The most effective method is using prepared statements and parameterized queries, which ensure that user input is treated as data rather than executable code.
Input validation and sanitization are also important to filter out malicious characters. Using stored procedures, escaping user input, and implementing least-privilege access for database accounts can further reduce risk. Regular security testing and code reviews help identify vulnerabilities early.
Role of Web Application Firewalls
Web application firewalls, also known as WAFs, provide an additional layer of protection against SQL injection attacks. They monitor incoming traffic and block suspicious requests before they reach the application.
While a WAF should not replace secure coding, it can help prevent attacks by filtering known malicious patterns and reducing exposure to automated attacks.
SQL Injection and SEO Impact
SQL injection attacks can also affect search engine optimization. A compromised website may display spam content, redirect users to malicious pages, or be flagged by search engines as unsafe.
This can lead to loss of search rankings, reduced traffic, and damaged brand credibility. Maintaining strong security helps protect not only user data but also website visibility and trust.
Conclusion
SQL injection is a serious security threat that continues to affect websites and applications worldwide. It exploits poor input handling and weak database interaction, making it both common and preventable.
By understanding how SQL injection works and implementing proper security measures, developers and organizations can protect their data and users. Secure coding, regular testing, and proactive defense strategies are essential to staying safe in an increasingly connected digital environment.





