
Hacking
The 10 Largest Ransomware Attacks in the history
Over the last decade, several high-profile attacks have caused millions or even billions of dollars in losses, disrupted critical operations, and compromised sensitive information.

Hacking
Over the last decade, several high-profile attacks have caused millions or even billions of dollars in losses, disrupted critical operations, and compromised sensitive information.
Hacking
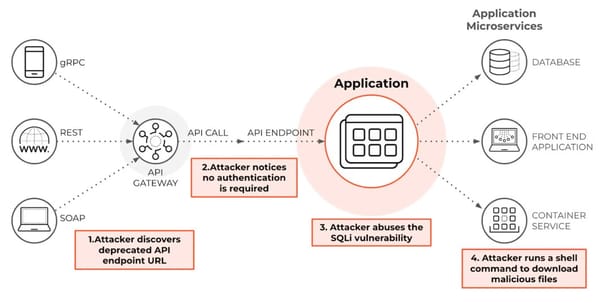
SQL Injection is a serious web security vulnerability that allows attackers to manipulate database queries by injecting malicious SQL code into user input fields. It works by exploiting applications that fail to properly validate or separate user input from executable SQL commands.
Hacking
Cross-site scripting, commonly known as XSS, is another frequent attack in WordPress websites. In this attack, malicious scripts are injected into web pages viewed by other users. When visitors load the affected page, the script executes in their browser.

Hacking
Managing different passwords for multiple services can be challenging. Password managers help by securely storing all passwords in one place, requiring you to remember only a master password.

Hacking
WhatsApp is designed primarily for personal messaging and casual communication. While it offers end-to-end encryption, it does not provide the structured access controls, audit trails, or centralized management that organizations require for sensitive information.

Hacking
Digital wallets and online banking have completely transformed the way money is transacted. Using mobile apps, QR codes, and the internet saves time and effort. However, this convenience and speed also create opportunities for cybercriminals. In recent years in Nepal, there have been numerous reported cases of fraud and hacking

Hacking
Unnecessary or poorly managed third-party plugins, open directory access, and misconfigured file permissions also increase hacking risk. In some cases, FTP access is left open, or databases are stored unencrypted, further compromising security.

Hacking
This post is dedicated to The Ministry of Education, Nepal and its digital practice in web. Ph.D. Research candidate working in similar sectors can become a part of it.

Hacking
A great mixture of political and social media influence which shows how few millions of data can be used to win an election of the entire country easily. The Data War and a documentary which has been shown in the such way that it helps to easily understand how we

Hacking
Digital footprint is a trail of data one creates while using the Internet. It includes the websites visited, emails sent, and information submitted to online services. A "passive digital footprint" is a data trail unintentionally left online. For Example, when visited a website it displays a message box

Hacking
Facebook Page hacking and admin takeovers have become increasingly common, especially through phishing scams and compromised personal accounts. This guide explains exactly what to do if someone takes control of your Facebook Page and how to recover it safely.

Hacking
Phishing campaigns primarily target email users across all platforms and rely heavily on sophisticated fake websites that closely mimic legitimate ones, combined with advanced email spoofing techniques that make the messages appear authentic and trustworthy to recipients.