Common attacks in WordPress
Cross-site scripting, commonly known as XSS, is another frequent attack in WordPress websites. In this attack, malicious scripts are injected into web pages viewed by other users. When visitors load the affected page, the script executes in their browser.
WordPress is one of the most widely used content management systems in the world, which makes it a frequent target for cyberattacks. Because of its popularity, open-source nature, and large ecosystem of plugins and themes, attackers often look for vulnerabilities in poorly configured or outdated installations.
Understanding the common attacks in WordPress is essential for website owners, developers, and administrators who want to protect their data, users, and reputation. Most WordPress attacks do not target the core software itself, which is regularly updated and generally secure, but instead exploit weak passwords, outdated plugins, insecure themes, or misconfigured hosting environments.
One of the most common attacks in WordPress is the brute force attack. In this type of attack, hackers attempt to gain access to the WordPress admin dashboard by repeatedly trying different username and password combinations. Since the default login URL is publicly known and often remains unchanged, attackers use automated bots to test thousands of password combinations in a short period of time.

If the website owner uses weak credentials such as “admin” as the username or simple passwords, the attacker may successfully gain access. Once inside, they can modify content, install malicious plugins, steal data, or even lock out the legitimate owner. Strong passwords, two-factor authentication, and limiting login attempts are effective defenses against brute force attacks.
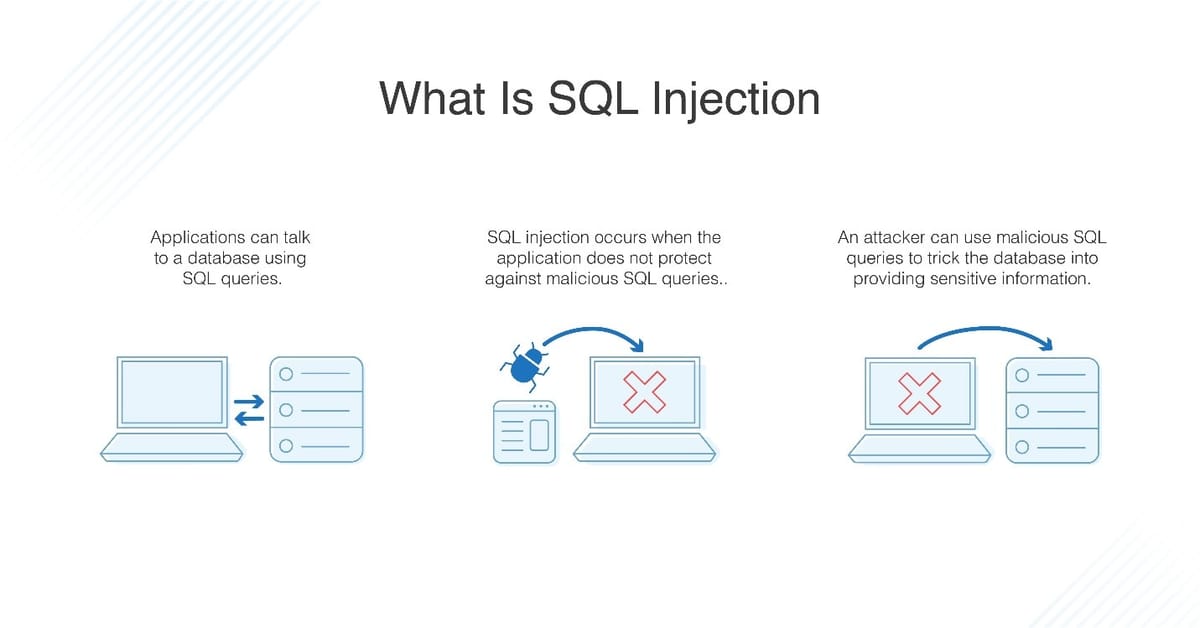
Another widespread threat is SQL injection. WordPress uses a database to store posts, user information, settings, and other content. SQL injection occurs when an attacker inserts malicious SQL code into input fields, such as search boxes or contact forms, to manipulate the database.
This type of attack is usually possible when plugins or themes fail to properly validate or sanitize user input. Through SQL injection, attackers can access sensitive information, modify data, or even gain administrative privileges. Keeping plugins updated and using well-coded themes significantly reduces the risk of SQL injection vulnerabilities.
Cross-site scripting, commonly known as XSS, is another frequent attack in WordPress websites. In this attack, malicious scripts are injected into web pages viewed by other users. When visitors load the affected page, the script executes in their browser.
This can lead to session hijacking, cookie theft, redirection to malicious websites, or unauthorized actions performed on behalf of users. XSS vulnerabilities often arise from insecure plugins or improperly handled form inputs. Regular updates, input validation, and using security plugins can help mitigate this threat.
Malware infections are also a major concern for WordPress websites. Attackers may upload malicious files to a server through vulnerable plugins, themes, or file upload forms. Once installed, malware can redirect visitors to spam websites, display unwanted advertisements, send spam emails, or steal user data. Some malware operates silently in the background, making it difficult to detect until significant damage has occurred.
In many cases, outdated software or nulled (pirated) themes and plugins are the entry points for malware. Using reputable sources for themes and plugins, maintaining backups, and performing regular security scans are crucial preventive measures.
File inclusion vulnerabilities represent another common type of WordPress attack. These occur when attackers exploit improperly coded plugins or themes to include unauthorized files from the server or remote sources. Remote File Inclusion (RFI) and Local File Inclusion (LFI) attacks can allow hackers to execute malicious code on the server.
This may lead to complete site takeover, data theft, or server compromise. Developers can prevent such attacks by ensuring proper coding practices, while site owners should minimize the number of installed plugins and remove unused components.

Distributed Denial of Service (DDoS) attacks also affect WordPress websites. In a DDoS attack, multiple systems flood a website with excessive traffic, overwhelming the server and causing it to slow down or crash. The goal is not necessarily to hack the site but to make it unavailable to legitimate users.
While WordPress itself is not uniquely vulnerable to DDoS attacks, poorly configured hosting environments may struggle to handle high traffic loads. Using content delivery networks (CDNs), firewalls, and scalable hosting solutions can help mitigate the impact of such attacks.
Another serious threat is privilege escalation. This occurs when a user with limited permissions, such as a subscriber or contributor, exploits a vulnerability to gain higher access rights, such as administrator privileges.
Once elevated, the attacker can modify site settings, install malicious code, or delete important content. Privilege escalation is often caused by poorly coded plugins that do not correctly check user roles and permissions. Keeping all components updated and using well-reviewed plugins can significantly reduce this risk.
Phishing and social engineering attacks are also common in the WordPress ecosystem. Attackers may trick site administrators into revealing login credentials through fake emails or login pages that mimic legitimate WordPress interfaces. Once credentials are stolen, the attacker can gain full control of the website. These attacks rely more on human error than technical vulnerabilities, making user awareness and education critical components of security.
Most of these threats exploit weak passwords, outdated plugins, insecure themes, or poor hosting configurations rather than flaws in the WordPress core. By maintaining regular updates, using strong authentication methods, installing security plugins, performing backups, and choosing reliable hosting providers, website owners can significantly reduce the risk of attacks and ensure a safer online presence.
In conclusion, while WordPress is a powerful and flexible platform, it is frequently targeted due to its popularity. Common attacks include brute force login attempts, SQL injection, cross-site scripting, malware infections, file inclusion vulnerabilities, DDoS attacks, privilege escalation, and phishing.






